
It came so, that after retirement my parents started to explore more benefits of technology, especially after when I left my iMac to them. As a techy person I was sure, that the equipment will be more than enough for them to serve almost any issue they needed. The main idea of leaving the very computer was a naive assumption from a point of view of a geek, that there is no need in any auxiliary software for maintaining optimal performance of the operating system.
Just about a week after my present for them I’ve started getting complaints about slower programs reaction, some extra popups, and other unwanted stuff. It was quite unusual for me. So next weekend I headed myself back to parents’ place. All the possible add-ons, different adware and unnecessary programs, downloaded and installed unknowingly with a bunch of games by my nephews too, overwhelmingly decreased ease of booting the system up. It took me a while to locate and clean-up manually operating system from the scrap.
The very next week everything repeated, with just a difference of my doing that time everything remotely. The third time was more than enough to push my search of any automated solution forward. I am more than aware, that techy people advise avoiding similar solutions for MacOS systems, however, for a shared home computer with several unskilled, curious and ordinary users there is no other way but using out-of-the-box tools.
After considering a huge amount of reviews, both negative and positive ones, containing valuable notes and details on variety of similar programs, I decided to go on with MacBooster from IOBit.
The main and the most convenient thing about the piece of software is the option to get it’s free version without general loss of available functionality and with opportunity to run regular cleaning and checking tasks by some simple and understandable actions, clicks and running logic for non-advanced users. Though the easy and same-name domain is available for downloading the software from http://www.macbooster.net, but the majority of reviews were leading to the http://www.iobit.com, where other interesting products are available from the same publisher. Another pleasant and interesting outcome was the presence of such tools like “Duplicate Finder”, “File Eraser” and “Photo Sweeper”.
Skipping download and standard installation warnings, dialogs and interactions parts of the process in current review, I would like to pass directly to the core functionality and interface.
The very first screen sets high expectations at once: so many promising functions, so many ways to improve workstation performance.

So, I started to explore all the menu options one by one.
The very first set of options is called “Security risks”. It groups Virus&Malware Scan, Realtime Protection and Privacy Clean subroutines.
Virus&Malware Scan searches for viruses, malware, system vulnerabilities and some user session setting files for suspicious files and treats. And it not only scans for the trojans, backdoors, scripts, but also provides functionality of proactive safeguarding through suspicious files samples uploading functionality, directly linking to the appropriate section of corresponding website.

Realtime Protection section is about protecting the system during all the period of uptime. It is achieved through securing processes in 8 main switchable modules: File System Shield, Web Shield, Download File Shield, Plugin Shield, Mail Shield, DNS Shield, Mac Login Shield and System Preferences Shield.

The most convenient moment of the modular structure is the functionality, allowing to enable or disable appropriate module upon necessity. It provides greater flexibility and supports better integration with other security tools or system security embedded opportunities.
The last section of Security Risks group is Privacy Clean routine. It scans all the online activity related information storages, including browsing and downloading data, application traces and unnecessary, mostly outdated logs. Again, the greatest flexibility of the tool comes from modular approach, allowing bypass or activate by switching on or off appropriate cleaning submodules.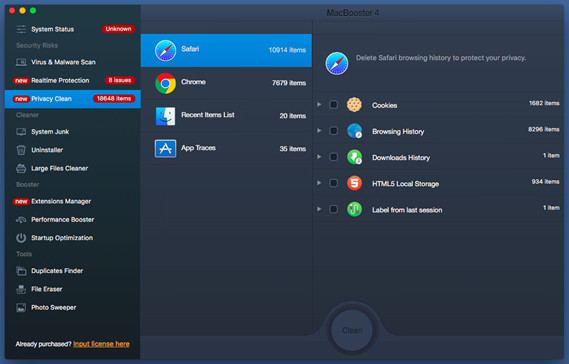
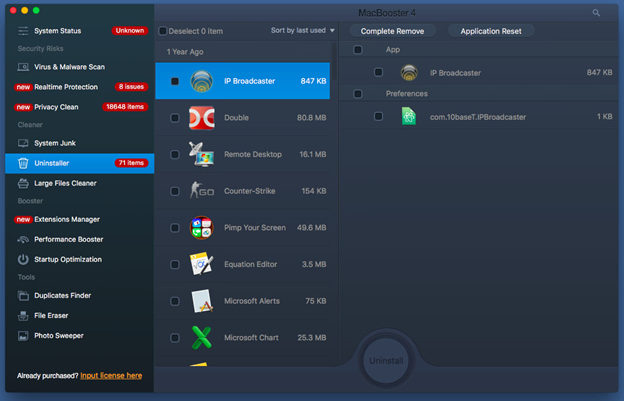
So, the next group of utilities is named “Cleaner”. It unites “System Junk”, “Uninstaller”, “Large Files Cleaner” submodules.

It searches for several places to find unused or unnecessary data, particularly Application Junk Files, System Cache Files, System Log Files, Broken Login Items and Mail Attachments.

Particularly, in my case it offered to remove a lot of stuff.

However, it should be treated selectively, by enabling or disabling appropriate options in “Details”, as, for example, “Mail Attachments” can contain some valuable information.
Uninstaller subsection is about removing uninstaller files for the majority of applications. Sometimes it happens, that after removing a piece of software from system the last file it leaves is the uninstaller script or program. For a system with frequent installations and removals of games and addons, the volume of such files can be big enough. Additionally, the subroutine offers to remove uninstallers for active programs too, as an option to free up some space.
And the final option speaks for itself – Large Files Cleaner. The utility locates and sorts all the files according to their size and offers to remove ones, selected by user.
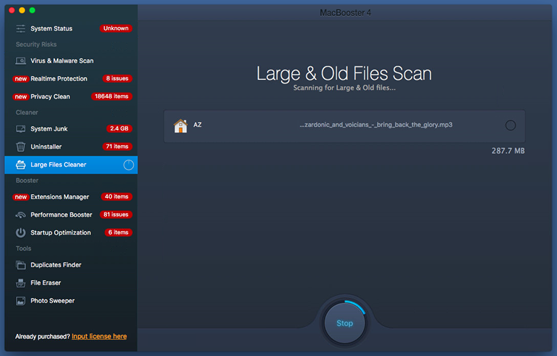
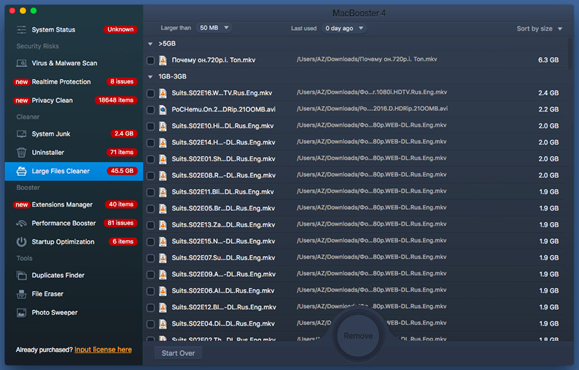
Upon selecting the unnecessary files and clicking “Remove” button, the appropriate data will be removed. So it leaves much to user’s decision and requires high attention.
Moving on we get to the “Booster” set of utilities, consisting of “Extensions Manager”, “Performance Booster” and “Startup Optimization”.
The very first subroutine is the “Extensions Manager”. This is probably the most important and the most required option for unskilled surfer, as majority of annoying software comes in the forms of addons, browser extensions and plugins, widgets and accelerators. The section allows to identify such extensions installed for each browser in the system, manually adjust the settings to switch appropriate functionalities on or off accordingly. 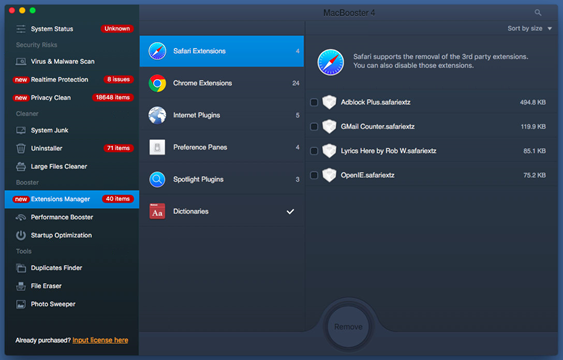
Still, majority of the functions are available separately for each browser in advanced mode, but from point of view of simplicity and integrated perception, MacBooster provides great comfort for coping with similar addendums.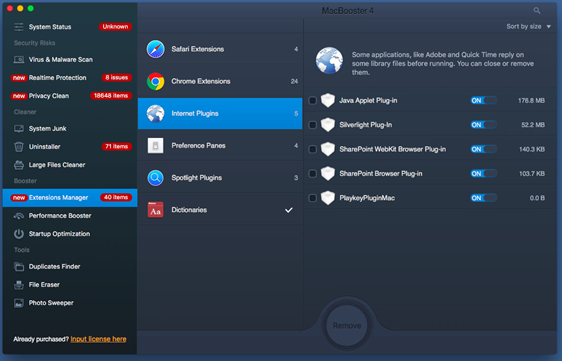
Though not all the extensions are malicious, there are many required and useful ones, hence it is necessary to pay attention to the details and approach deleting the addon wisely.
Performance Booster is trying to improve the way workstation works by launching “Application Optimization”, “RAM Optimization”, and “Disk Permission Fix” modules.

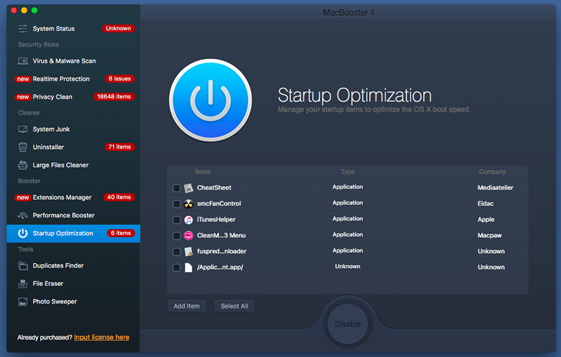
“Startup Optimization” subroutine is intended for manually adding and removing applications to start with system boot. It is very useful for locating initial processes and agent programs for sending private and sensitive user data.
And finally we get to previously mentioned tools like “Duplicate Finder”, “File Eraser” and “Photo Sweeper”.
These tools are quite useful not only for regular users, but for experienced ones too, as they optimize not just technically, but provide some higher, logical level of service. It is quite important sometimes to move, backup and restore data in between folders and devices. And often some data remains duplicated and forgotten. Within time such doubled data gets bigger in total volumes. “Duplicate Finder” is searching for such information throughout all the connected and mounted hard drives, grouping output files by same internal content.
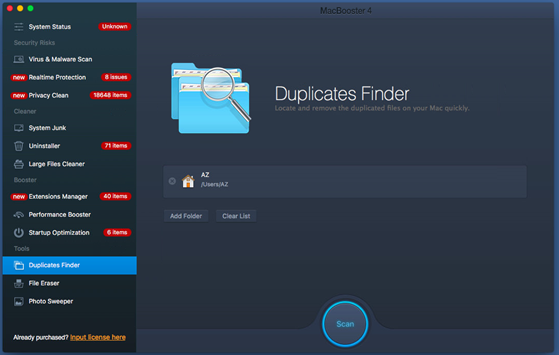
Upon finding and grouping duplicate content data, user is provided with opportunity to delete extra copies depending on information of time and location of the files.
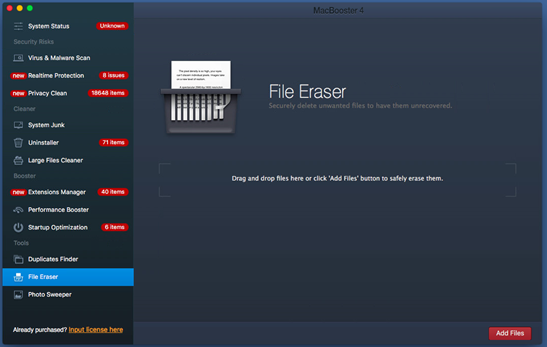
“File Eraser” is a drag-and-drop subsection to completely destroy contents of the file in a way, that no other software can recover it to an assumingly acceptable state. It is very important if some sensitive data is being processed on the workstation or the file contains viruses, trojans and other vulnerable content.
Another option to lessen occupied hard drive volume is to find similar or duplicate photos, which are hard to find by Duplicate Finder, such as rotated, resized, quick-shot set of photos.
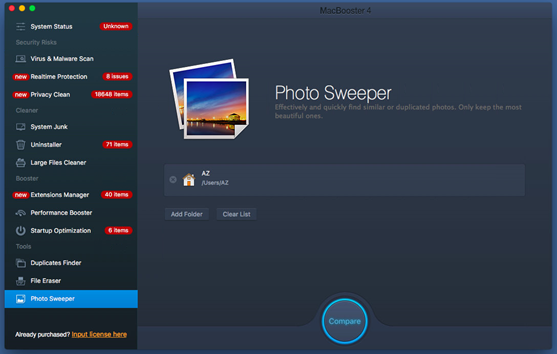
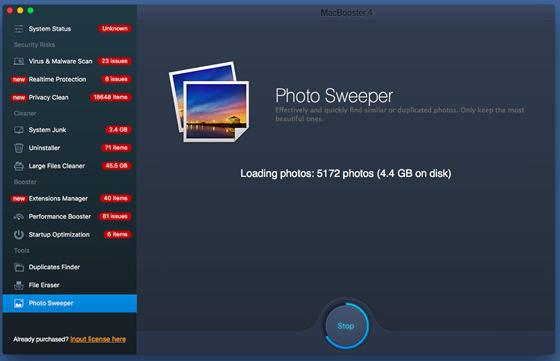
First it scans and locates all the photos on the accessible hard drives.
And after conducting a thorough and deep search, it displays all the groups of identical files.
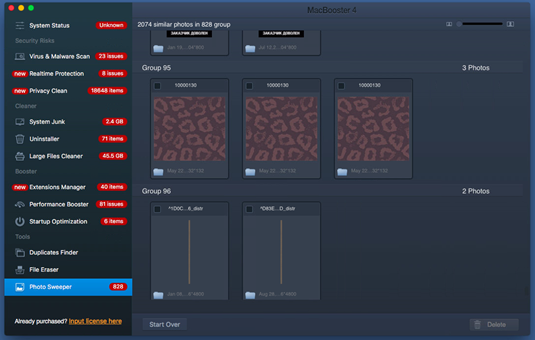
The rest of activity is up to the user’s decision whether to keep or erase extra or similar copies of photos located.
Having considered all the core functions, it is time to draw a bottom line for the review.
Pros:
- Though majority of functions are available separately through system and application, MacBooster is a very convenient graphical user interface solution for all-in-one MacOS operating system environment management and tuning-up.
- Well-structured and intuitively understandable set of utilities.
- Real-time protection and activity scanning.
- Fast and reliable service: except for the last 3 bonus tools – all the checkups, scans and inspections were performed almost instantly.
- Deep and thorough search of duplicates files and similar photos, drag-and-drop shredder – a functionality every family and office computer needs.
- Flexibility and total control over settings erasure, addendum and modification.
Cons:
So far only one note to be provided: some extra text description is missing next to the functions, probably some hints and popups for “dummy” users, preferring to get advantage of integrated GUI solution instead of going deep and digging into system settings and tools.
Conclusion:
MacBooster is a very useful and comfortable in use toolset for maintaining MacOS system fast and reliable performance on high level of productivity. The IOBit piece of software is a valuable addition for any home and office workstation, which is mostly used for surfing the net, data manipulation and online gaming activities secure, stable and satisfactory implementation. I would highly recommend having the application on every personal MacOS instance.
Get MacBooster to Clean and Speed up Your Mac
Leave a Reply